DomainRelationShips
██╗ ██╗ █████╗ ██╗██████╗
██║ ██║██╔══██╗ ██║██╔══██╗
██║ ██║███████║█████╗██║██║ ██║
██║ ██║██╔══██║╚════╝██║██║ ██║
╚██████╔╝██║ ██║ ██║██████╔╝
╚═════╝ ╚═╝ ╚═╝ ╚═╝╚═════╝
██████╗ ██████╗ ███╗ ███╗ █████╗ ██╗███╗ ██╗███████╗
██╔══██╗██╔═══██╗████╗ ████║██╔══██╗██║████╗ ██║██╔════╝
██║ ██║██║ ██║██╔████╔██║███████║██║██╔██╗ ██║███████╗
██║ ██║██║ ██║██║╚██╔╝██║██╔══██║██║██║╚██╗██║╚════██║
██████╔╝╚██████╔╝██║ ╚═╝ ██║██║ ██║██║██║ ╚████║███████║
╚═════╝ ╚═════╝ ╚═╝ ╚═╝╚═╝ ╚═╝╚═╝╚═╝ ╚═══╝╚══════╝
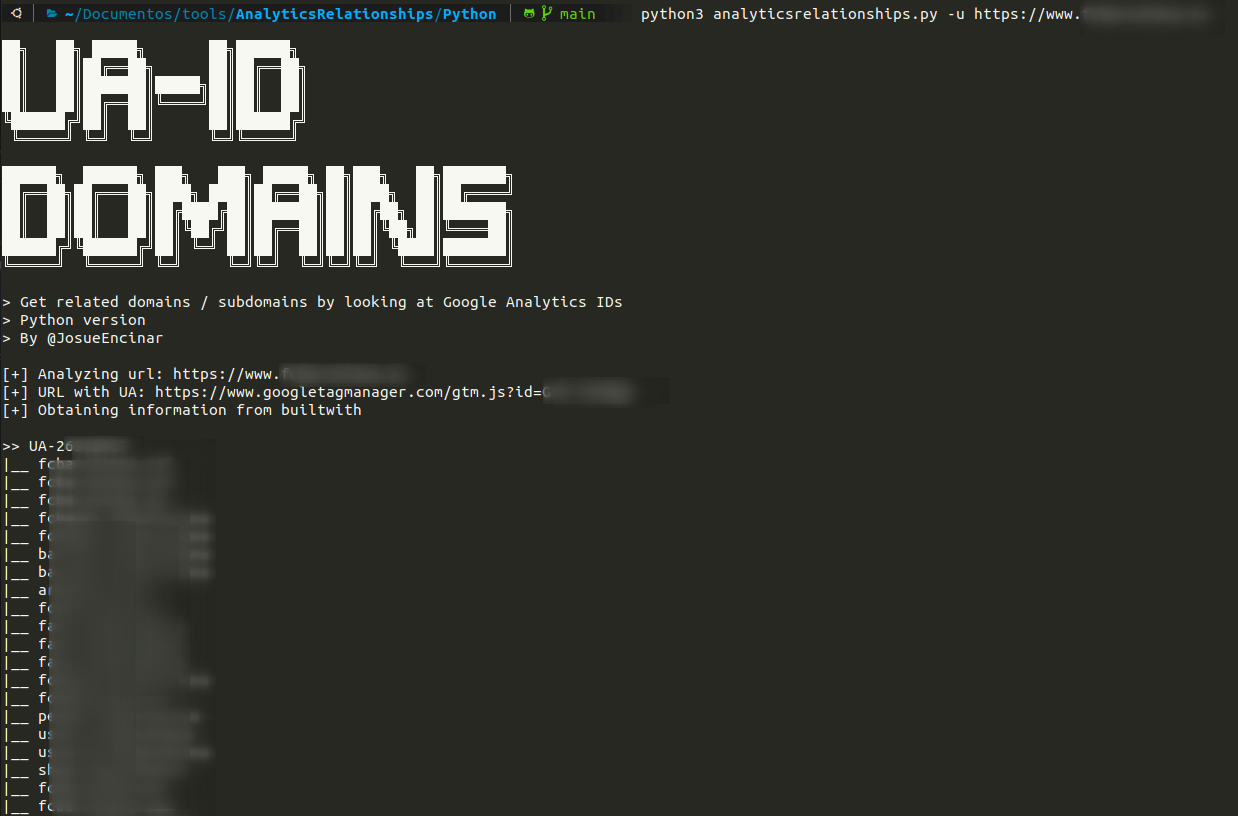
> Get related domains / subdomains by looking at Google Analytics IDs
> Python/GO versions
> By @JosueEncinar
This script try to get related domains / subdomains by looking at Google Analytics IDs from a URL. First search for ID of Google Analytics in the webpage and then request to builtwith and hackertarget with the ID.
Note: It does not work with all websites.It is searched by the following expressions:
-> "www\.googletagmanager\.com/ns\.html\?id=[A-Z0-9\-]+"
-> GTM-[A-Z0-9]+
-> "UA-\d+-\d+"
Available versions:
Installation:
Installation according to language.
Python
> git clone https://github.com/Josue87/AnalyticsRelationships.git
> cd AnalyticsRelationships/Python
> sudo pip3 install -r requirements.txt
GO
> git clone https://github.com/Josue87/AnalyticsRelationships.git
> cd AnalyticsRelationships/GO
> go build -ldflags "-s -w"
Docker
> git clone https://github.com/Josue87/AnalyticsRelationships.git
> cd AnalyticsRelationships
> docker build -t analyticsrelationships:latest .
Usage
Usage according to language
Python
> python3 analyticsrelationships.py -u https://www.example.com
Or redirect output to a file (banner or information messages are sent to the error output):
python3 analyticsrelationships.py -u https://www.example.com > /tmp/example.txt
GO
> ./analyticsrelationships --url https://www.example.com
Or redirect output to a file (banner or information messages are sent to the error output):
> ./analyticsrelationships --url https://www.example.com > /tmp/example.txt
Docker
> docker run -it analyticsrelationships:latest https://www.example.com
Or redirect output to a file (banner or information messages are sent to the error output):
> docker run -it analyticsrelationships:latest https://www.example.com > /tmp/example.txt
Examples
Python
Output redirection to file /tmp/example.txt:
Without redirection:
GO
Without redirection:
Working with file redirection works just like in Python.
Author
This project has been developed by:
- Josué Encinar García -- @JosueEncinar
Disclaimer!
This is a PoC. The author is not responsible for any illegitimate use.